Personal Due Diligence Report
James R. Peterson
Personal due diligence / identity verification report
Client requested verification of identity continuity, professional credibility, public-risk factors, and hidden exposure before extending deeper personal and practical trust.
Client request
Is this person who he says he is, does his background check out, and are there public risk signals I should care about?
Analyst conclusion
Identity continuity is strong and the professional history broadly checks out, but recent visibility growth and credential exposure justify caution and continued monitoring.
Handling note
- Exact residence lines, dependent names, and full personal identifiers remain masked in the web version.
- Findings reflect open-source review completed through November 28, 2025 and do not include subpoena-only or institution-only records.
- Any protected medical, banking, or device-level material would require separate authorization and is outside this sample file.
Risk conclusion
Moderate
Driven mainly by breach exposure and the recent visibility spike around the consulting launch.
Confidence level
High
Identity continuity and professional history are supported across multiple independent public surfaces.
Reviewed findings
27
14 high-confidence findings across identity, records, business, and cyber review.
Attached exhibits
5
Portrait, summary, records, risk, and monitoring exhibits are attached to support the written findings.
Summary below is based on public-source review completed between November 16, 2025 and November 28, 2025.
Pages 1-2
Cover sheet and executive summary
Subject portrait
Primary identity image

Primary identity image matched against professional and social surfaces reviewed in this file.
Page 5
Legal records and breach exposure
Page 8
Monitoring appendix
FILE_CONTENTS
SCOPE_OF_REVIEW
The file was built to answer four client questions before any decision to deepen trust.
- Does James R. Peterson resolve to one stable real-world identity across names, phones, emails, residences, and household context?
- Do the work history, conference traces, technical footprint, and October 2025 consulting launch support the public career narrative?
- Are there legal, civil, financial, cyber, or reputational issues that should materially affect trust?
- What remains unverified, and what practical actions should follow from the current file?
Section
01
01 CASE SUMMARY
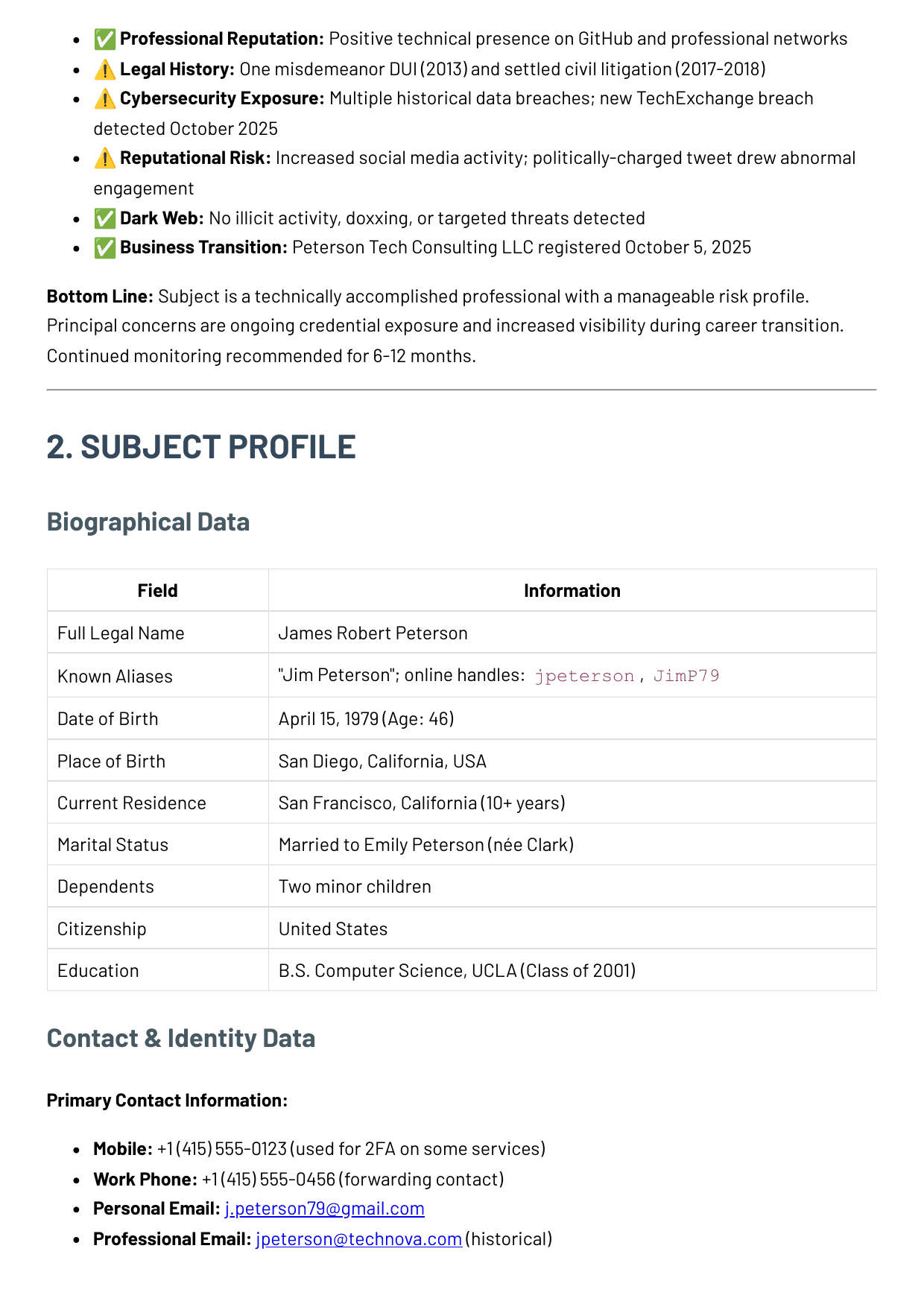
Case summary
Start with the client's question, the bottom-line answer, the confidence level, and the top concerns that matter most before the reader scans the rest of the file.
Case type
Personal due diligence / identity verification
Overall confidence
High
Client question
Is this person who he says he is, does his background check out, and are there public risk signals I should care about?
Bottom-line answer
Identity continuity is strong and the professional history broadly checks out, but recent visibility growth and credential exposure justify caution and continued monitoring.
What was verified
- Identity continuity across public records, professional profiles, and business registration is strong.
- Professional background is broadly consistent with how the subject presents himself.
- No evidence of bankruptcy, active judgments, or ongoing criminal proceedings was found.
- The October 2025 consulting launch is corroborated by registry and platform updates.
What raised concern
- The personal email appears in multiple historical breaches and a new TechExchange leak.
- The October 22 policy-related X post increased hostile engagement and public visibility.
- The new consulting entity creates a fresh public attack surface and reputation layer to monitor.
- MFA usage and broader password-hygiene maturity remain unclear from open-source review.
What remains unknown
- No public evidence confirms how financial accounts and critical mailboxes are secured today.
- The scale of the consulting client pipeline is still too early to verify from public sources.
- Household exposure is intentionally only partially represented in the public-facing preview.
- No public-source review can rule out all private conduct, only what leaves a visible trail.
Section
02
02 KEY FINDINGS
Key findings
Show the most important findings in plain English before asking the reader to absorb detailed evidence.
Identity continuity is strong
Names, aliases, phones, emails, and residence history resolve to one coherent Bay Area identity.
Professional background is broadly verified
A twenty-year technology career, conference traces, and technical footprint align with the stated work history.
Breach exposure remains the main cyber concern
Multiple historical breach appearances plus a fresh TechExchange leak were tied to the subject's long-used email.
Public visibility increased in October 2025
The consulting launch and public commentary created a sharper monitoring load than the earlier baseline period.
Resolved legal history still matters
A historical DUI and one settled civil dispute remain relevant context even though no active litigation was found.
No active targeting was identified
No doxxing packages, identity kits, or underground threat references were located in the reviewed sample.
Section
03
03 SUBJECT SNAPSHOT
Subject snapshot
Present the person quickly: who he is, where he lives, household context, and the identity anchors that make the subject feel real.
Biographical data
The primary identity anchors that define who the subject is.
Full legal name
James Robert Peterson
Known aliases
"Jim Peterson"; online handles: jpeterson, JimP79
Date of birth
April 15, 1979 (Age 46)
Place of birth
San Diego, California, USA
Current residence
San Francisco, California (10+ years)
Citizenship
United States
Education
B.S. Computer Science, UCLA (Class of 2001)
Household and residence context
Family and home continuity, shown without overexposing private specifics.
Marital status
Married to Emily Peterson (nee Clark)
Dependents
Two minor children
Property ownership
James and Emily Peterson; purchased 2014
Previous addresses
Sunnyvale (2008-2014), San Jose (2005-2008), Los Angeles (1998-2005)
Family exposure note
Public family content is limited, but profile continuity and photo updates remain observable.
Relationship context
Known household relationships relevant to continuity and risk review.
Spouse
Emily Peterson - Referenced in household and property continuity traces.
Dependents
Two minor children - Mentioned in family-context surfaces, but the preview should avoid exposing specifics.
Section
04
04 IDENTITY AND CONTACT TRAIL
Identity and contact trail
Show aliases, usernames, phones, emails, and address continuity so the reader can see how the identity was tied together.
Identity pivots
These are the identifiers that allowed the analyst to connect the subject across breach, profile, household, business, and continuity surfaces.
Primary mobile
+1 (415) 555-0123
Repeated across people-search and account-recovery references.
Work forwarding line
+1 (415) 555-0456
Appears on historical company contact traces and consulting site references.
Personal email
Strongest identity pivot and the address tied to multiple breach datasets.
Historic corporate email
Consistent with the CTO tenure at TechNova.
Business email
Active on the new consulting domain and tied to the LLC launch period.
Primary domain
petersontechconsulting.com
Registered in early October 2025 as the public-facing consulting identity.
Continuity chain
2001-06
Education and alumni continuityUCLA identity anchor
Education timing anchors the earliest stable public identity and matches the early Los Angeles period.
2014-08
Property and household tracesSan Francisco residence continuity
Residence and household continuity reinforce that the subject has been stably anchored in San Francisco for more than a decade.
2019-10
Employer-side biographies and cached press materialTechNova executive phase
Third-party company references support the CTO claim independently of self-authored social profiles.
2025-10-05
State business registryLLC registration links identity to new business
The consulting launch attaches the subject's legal name to a fresh public business surface with matching contact details.
2025-10-15
LinkedIn and public web reviewProfile transition matches registry timing
The professional profile update, consulting domain, and business formation all align inside the same October window.
Address history
The residence trail that supports long-term continuity.
2014 - present
San Francisco, California - Current long-term residence area; exact street intentionally withheld in the public preview.
2008 - 2014
Sunnyvale, California - Appears in address-history aggregators and older directory traces.
2005 - 2008
San Jose, California - Matches the GammaSoft employment window.
1998 - 2005
Los Angeles, California - Consistent with UCLA attendance and early-career location.
Alias and household context
Names, handles, and household continuity that keep the identity coherent.
Preferred name
Jim Peterson
Public aliases
James R. Peterson, Jim Peterson
Known usernames
jpeterson, JimP79, @JimPeterson
Household summary
Married to Emily Peterson with two minor children; long-term Bay Area residence pattern is consistent with career history.
Relationship context
Known household relationships relevant to continuity and risk review.
Spouse
Emily Peterson - Referenced in household and property continuity traces.
Dependents
Two minor children - Mentioned in family-context surfaces, but the preview should avoid exposing specifics.
RELATIONSHIP_MAPPING_PROOF
How the report packages relationship and location corroboration
The delivered report keeps graph-style reasoning and geography checks inside the same evidence narrative, so the client sees why a relationship or location clue was accepted instead of reading a disconnected capability list.
Relationship-mapping readout
- Household, alias, and residence continuity are shown together so the reader can see which people and entities belong in the same evidence chain.
- Business registration timing is evaluated against the same address and contact anchors to show whether a new entity is genuinely attached to the subject.
- The report distinguishes stable continuity from speculative linkage by naming which relationships are directly supported by records and which remain contextual only.
Geospatial corroboration notes
- Address history is presented as a continuity trail rather than a raw dump, making long-term Bay Area stability legible at a glance.
- Timeline events and residence anchors are reviewed together so impossible-travel or geography contradictions can be surfaced when they appear.
- IP, Wi-Fi, and landmark clues matter only when they agree with the rest of the case file; isolated location hints stay low-confidence until corroborated.
Identity review notes
- Alias usage is stable: James R. Peterson, Jim Peterson, jpeterson, and JimP79 all resolve into one coherent footprint rather than separate conflicting personas.
- Phone, email, and residence history reinforce each other across people-search, breach, company, and social surfaces.
- Household context is present and consistent, but dependent names and exact street data stay intentionally redacted in the web report.
- The strongest identity continuity comes from agreement between professional surfaces, household traces, and the October 2025 business launch.
Evidence anchors
The identity conclusion is not based on one source. These are the main cross-checks that reinforce the same person over time.
Open web search aggregation
High confidenceName, San Francisco location, TechNova role, and consulting launch resolve to one coherent adult identity.
The subject does not look fabricated or split across conflicting identities.
People-search aggregators
Medium confidencePhone numbers, age band, San Francisco residence pattern, and historical Bay Area moves align across aggregator traces.
The subject has a stable adult footprint rather than disposable identifiers.
Property / assessor continuity
Medium confidenceOwnership continuity supports long-term San Francisco residence for James and Emily Peterson.
The subject appears settled and real-world anchored, not transient or hard to place.
Household continuity traces
Medium confidenceEmily Peterson appears as spouse in multiple household and property-adjacent traces.
The family profile looks stable and consistent with the subject's public identity.
Wayback snapshots of TechNova biography pages
Medium confidenceArchived versions preserve the subject's title progression and public biography language.
The subject's public story has continuity over time, not just recent polish.
Section
05
05 PROFESSIONAL FOOTPRINT
Professional footprint
Employment history, technical credibility, and public career evidence belong here, separated from lifestyle and social behavior.
Employment history
This is the verified career backbone behind the subject's public identity.
Oct 2019 - Oct 2025
TechNova Inc. - Chief Technology Officer
San Francisco, CA
2010 - 2019
Innotech Corp. - Senior Software Engineer
Palo Alto, CA
2005 - 2010
GammaSoft LLC - Software Developer
San Jose, CA
2001 - 2005
Junior engineering roles
Los Angeles, CA
Professional readout
- Archived TechNova biographies preserve the CTO title and San Francisco base before the current report window.
- Conference speaker pages repeat the same cloud-infrastructure specialization and executive framing seen on LinkedIn.
- No patent or research-profile trail was found, which is consistent with an operator role rather than an academic or inventor profile.
- The October 2025 LLC registration matters because it turns the career pivot into a real legal and business event.
jpeterson
This is the strongest public source for role verification, network continuity, and timing of the consulting transition.
- Profile reflects a move from TechNova CTO to Peterson Tech Consulting on Oct 15, 2025.
- Connection count remains above 500 with endorsements concentrated in cloud infrastructure, architecture, and leadership.
- The Oct 20 transition post drew roughly 150 reactions and 40 comments, reinforcing that the career change was public and recognized.
GitHub
jpeterson
GitHub helps distinguish a real engineering background from a résumé-only identity.
- Public repositories span Go, Python, TypeScript, and Terraform, which fits the infrastructure-heavy career story.
- Last visible public commit activity sits in mid-2024, suggesting a senior operator with lower public coding volume in the CTO phase.
- No obvious public secret leakage or exposed tokens were observed in the accessible repositories.
LinkedIn profile review
Observed Nov 28, 2025Source sheet
LinkedIn profile capture
Filed note
Captured during the Nov 28, 2025 review to confirm role chronology, network size, and the October consulting transition.
Surface
LinkedIn profile review
Observed
Observed Nov 28, 2025
Reference
PF-01
Purpose
Primary professional anchor
Profile name
James R. Peterson
Handle
linkedin.com/in/jpeterson
Headline
Founder, Peterson Tech Consulting LLC | Former CTO, TechNova
Region
San Francisco Bay Area
Connections
500+
Followers
1,486
Recent profile edit
Oct 15, 2025
Experience
- Peterson Tech Consulting LLC · Founder · Oct 2025-present
- TechNova Inc. · Chief Technology Officer · Oct 2019-Oct 2025
Featured
- Career-transition post dated Oct 20, 2025
- Consulting domain added to profile contact card
Analyst note
Profile chronology, stated location, and October transition timing match the registry and archived employer material.
Independent public references
These traces support the professional story without relying only on self-maintained profiles.
LinkedIn profile
High confidenceLinkedIn profile reflects the move from TechNova CTO to Peterson Tech Consulting with 500+ connections.
His work history appears real and professionally legible rather than improvised.
GitHub public profile
High confidencePublic repositories and commit history align with the subject's engineering background.
The engineering career is supported by real technical traces, not just polished bios.
TechNova executive bio / press archive
High confidenceArchived company materials identify James R. Peterson as CTO based in San Francisco.
The senior-title claim is backed by public employer-side material.
Conference speaker pages
Medium confidenceSpeaker biographies on engineering events repeat the TechNova role and cloud-infrastructure expertise.
He presents like a real mid- to senior-level technology operator with public visibility.
LinkedIn post archive
High confidenceA public "moving on" announcement drew strong positive engagement from the professional network.
The transition appears legitimate and publicly recognized, not hidden or fabricated.
Wayback snapshots of TechNova biography pages
Medium confidenceArchived versions preserve the subject's title progression and public biography language.
The subject's public story has continuity over time, not just recent polish.
Section
07
07 IMAGES AND VISUAL EVIDENCE
Images and visual evidence
A consumer report should show the subject and the report artifact visually, not only describe them.
Image continuity log
The available public imagery is limited, but the same likeness repeats across professional, corporate, social, and business surfaces. That consistency is a useful identity signal on its own.

LinkedIn profile photo
Observed Oct 15, 2025Professional headshot
Used as the main profile image during the consulting transition update.
Supports continuity between the CTO identity and the new consulting identity.

TechNova biography archive
Observed via archive Feb 14, 2024Executive biography portrait
Same facial image family and grooming style as the professional profile surface.
Shows the public identity did not appear suddenly during the 2025 launch window.

Facebook profile update
Observed Oct 25, 2025Casual profile-photo refresh
Public layer is limited, but the visible profile image remains consistent with the primary likeness.
Adds continuity without materially increasing reputational concern.

Consulting website contact panel
Observed Nov 1, 2025Founder profile image
Business-facing image stays visually aligned with the same public identity already seen on professional surfaces.
Reduces the chance that the consulting launch is fronted by a conflicting or fabricated persona.
Extract
Subject profile extract
Observed
Source file page 2
Reference
EXT-01
Purpose
Identity sheet crop
Shows how the file handles portrait, aliases, phones, emails, and residence context together.
Extract
Court and records extract
Observed
Source file page 5
Reference
EXT-02
Purpose
Records and court crop
Pulls the reader closer to the public-record findings instead of relying only on a full-page exhibit.
Extract
Risk matrix extract
Observed
Source file page 6
Reference
EXT-03
Purpose
Risk matrix crop
Shows the scored risk logic in tighter detail so the written conclusion feels sourced.
Extract
Monitoring alert extract
Observed
Source file page 8
Reference
EXT-04
Purpose
Monitoring appendix crop
Brings the monthly alert cadence closer to the reader without making them inspect a full appendix page.
Public image set reviewed
Four public-facing images were reviewed across professional, social, and business surfaces. Taken together, they support continuity of likeness rather than a conflicting public persona.
IMG-01
Observed Oct 15, 2025
LinkedIn profile and archived employer biography

Primary profile image
Used as the main comparison anchor for likeness continuity across the rest of the reviewed public image set.
IMG-02
Observed via conference archive Jun 11, 2024
Conference speaker page
Conference speaker portrait
Professional event portrait consistent with the executive bio and LinkedIn image family.
IMG-03
Observed Oct 25, 2025
Facebook public layer
Casual profile update
Lower-signal social photo that supports continuity without materially changing the risk picture.
IMG-04
Observed Nov 1, 2025
Consulting site profile panel
Founder headshot
Business-facing portrait aligned with the same public likeness used across professional surfaces.
Exhibit A
Source PDF Pages 1-2Cover sheet and executive summary
Why this exhibit matters
Cover sheet and opening summary
Classification, subject identity, table of contents, and headline risk framing.
- Shows the classified file treatment and opening summary structure the page is now emulating.
- Anchors the cover-sheet language used in the first screen of the web version.
- Supports the shift away from generic marketing intro copy.
Exhibit B
Source PDF Page 2Subject profile and contact pivots
Why this exhibit matters
Subject profile and pivot sheet
Biographical data, aliases, phones, emails, and residence handling from the source dossier.
- Provides the strongest source image for the subject snapshot and identity-contact sections.
- Shows how aliases, phones, emails, and residence handling are presented in the original file.
- Makes the identity section feel sourced from a real dossier page.
Exhibit C
Source PDF Page 5Legal records and breach exposure
Why this exhibit matters
Records, registry, and breach evidence
Civil and criminal findings, business registration, and the breach summary table in one evidence block.
- Connects public-record findings to the breach table inside one documentary evidence block.
- Supports both the legal-history and cyber sections without abstracting the underlying file.
- Carries some of the strongest trust-impacting data in the report.
Exhibit D
Source PDF Page 6Risk evaluation
Why this exhibit matters
Risk score and movement logic
Risk matrix, score movement, and scenario forecasting as presented in the PDF.
- Shows the actual risk matrix that drives the written conclusion.
- Keeps the score movement visible as a document exhibit rather than only as styled table copy.
- Reinforces that the final risk conclusion came from a scored review process.
Exhibit E
Source PDF Page 8Monitoring appendix
Why this exhibit matters
Monthly monitoring review
Monthly monitoring roll-up with the alert log that pushed the score from 5/10 to 6/10.
- Shows the alert cadence that made the October 2025 period materially different from the earlier baseline.
- Brings the ongoing monitoring story closer to how a delivered appendix would actually read.
- Lets the reader see platform and breach changes in one reviewed appendix capture.
Section
08
08 PUBLIC RECORDS AND LEGAL HISTORY
Public records and legal history
Legal, civil, and financial history should be explicit, contextualized, and separated from cyber or business evidence.
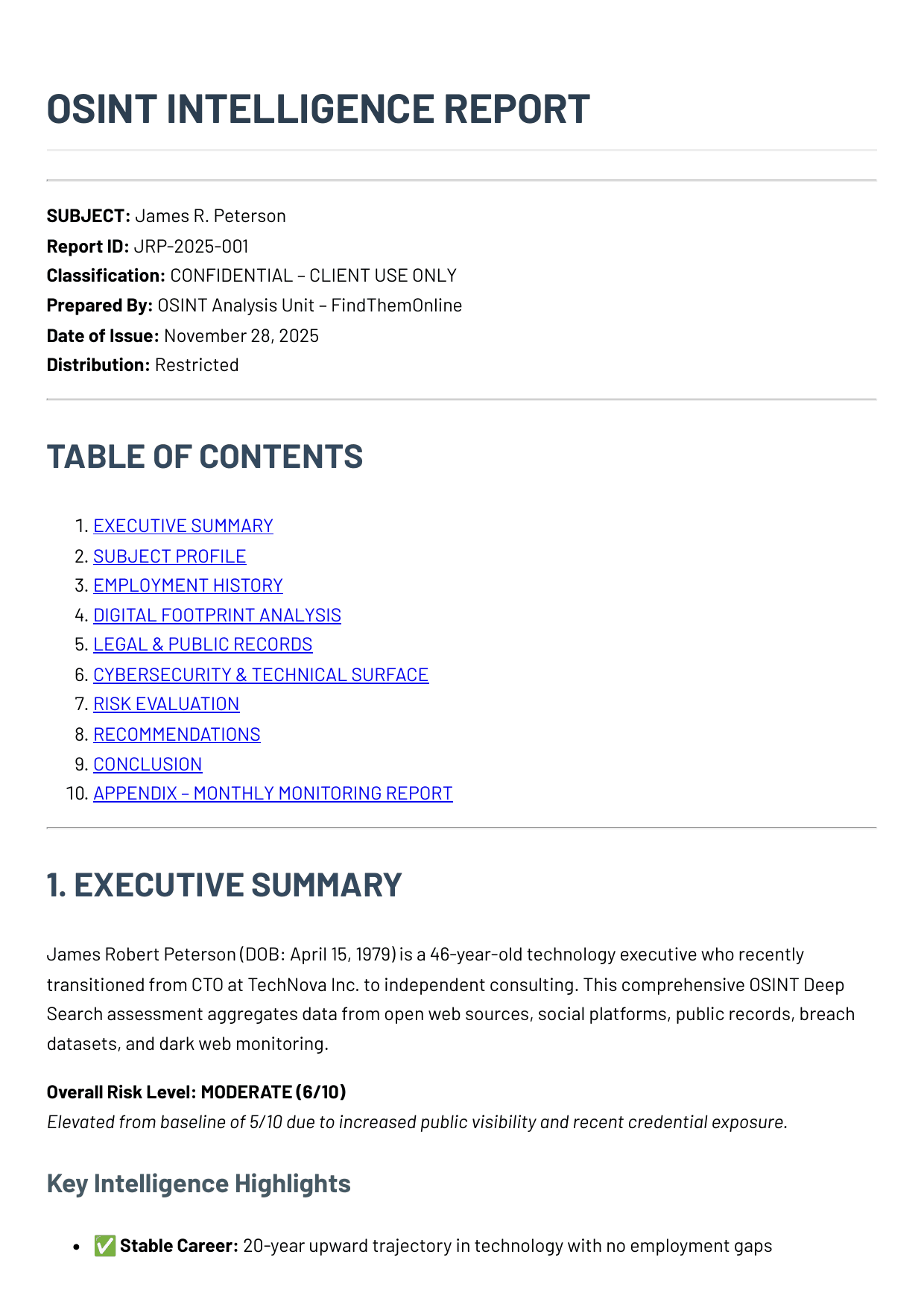
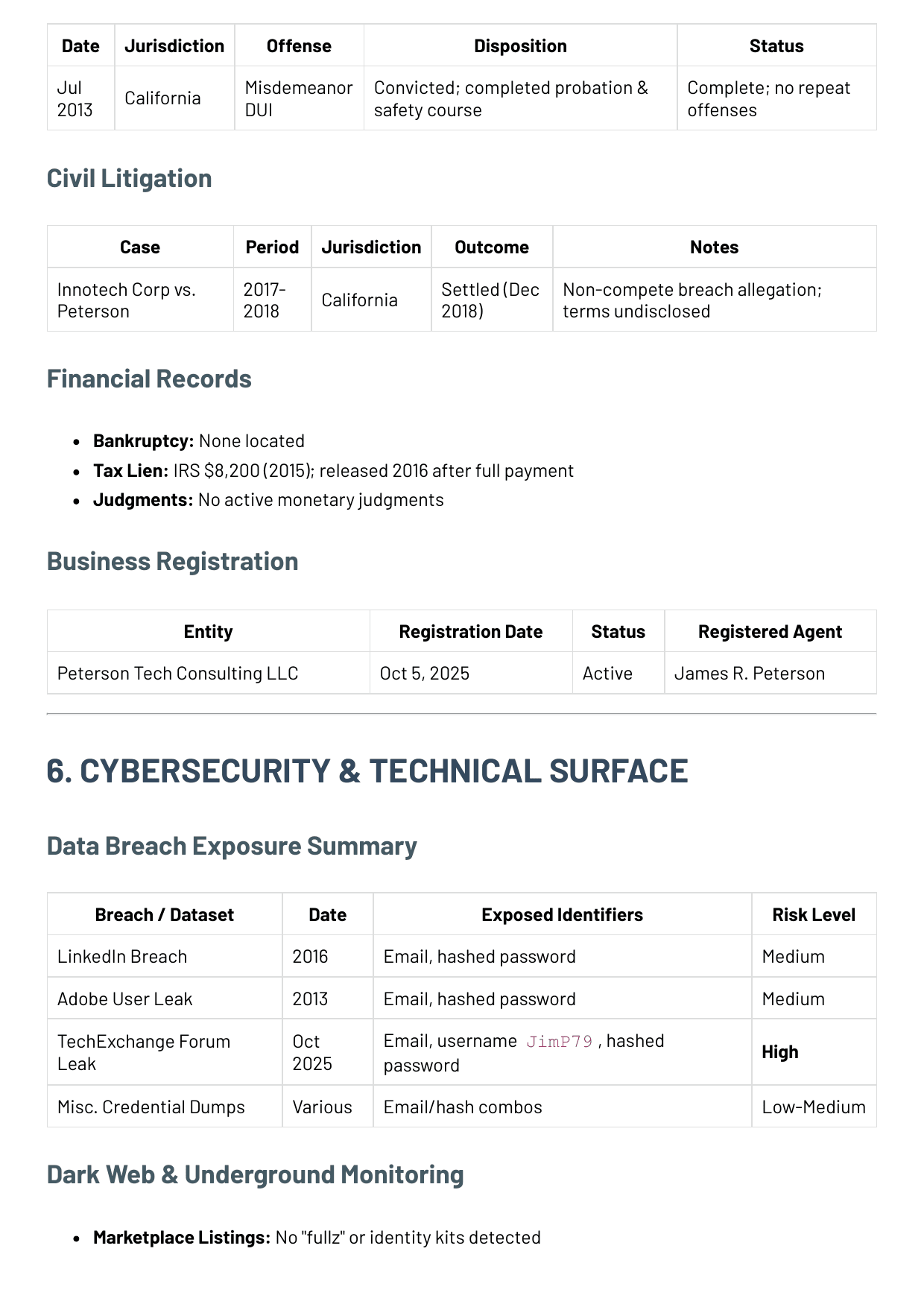
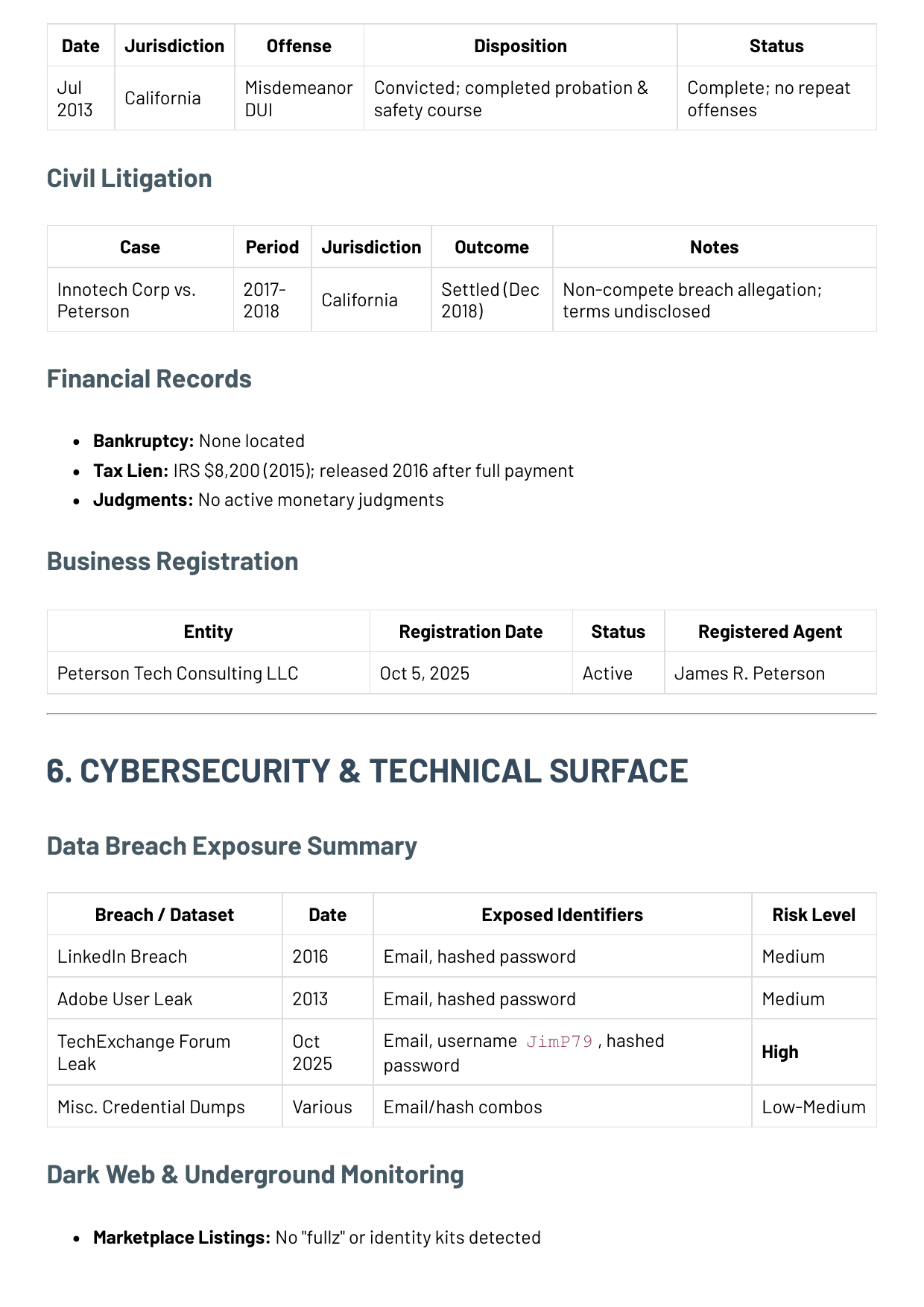
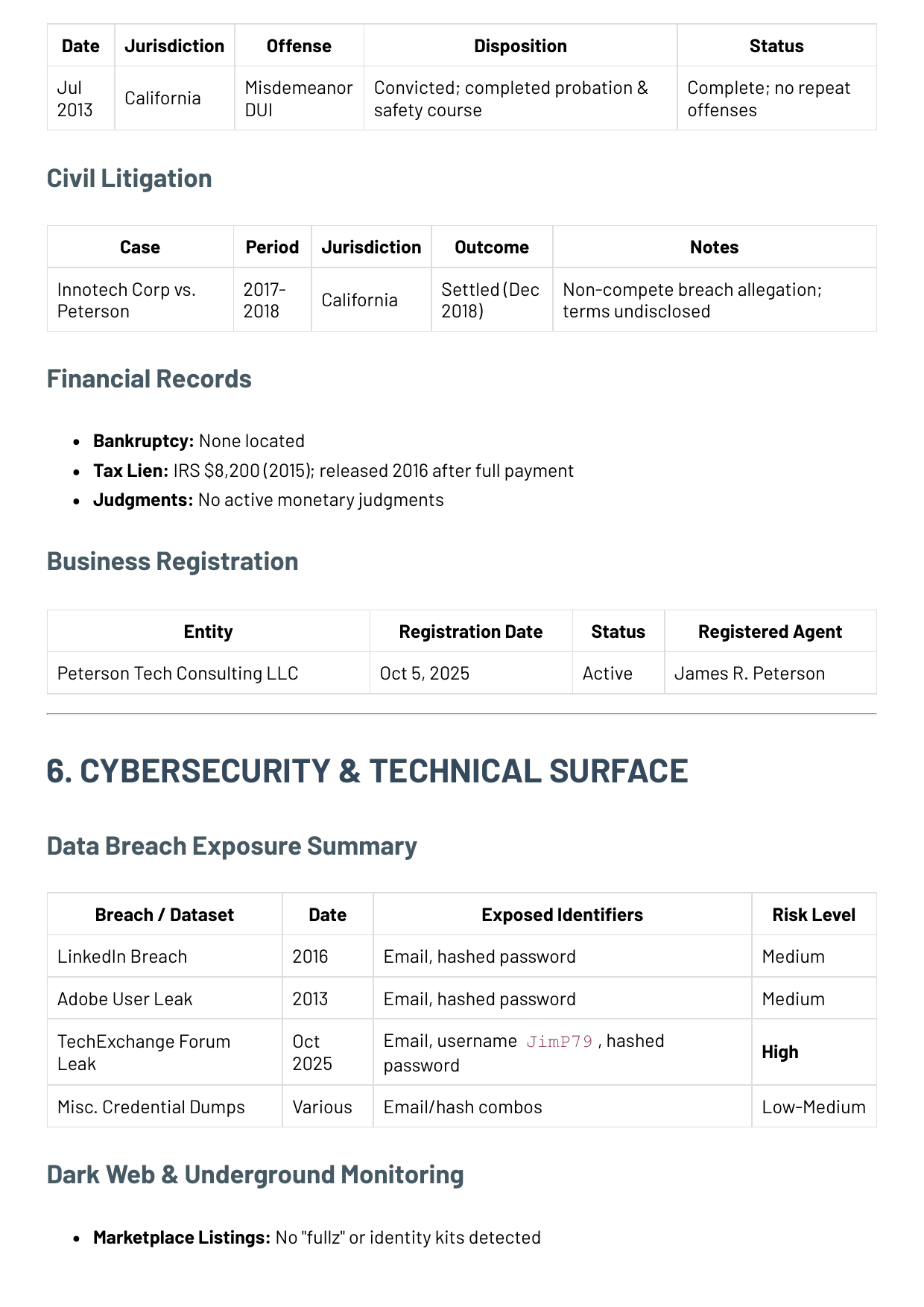
Misdemeanor DUI
State criminal court index
Single DUI matter located in California criminal-court records during the subject's Innotech period.
Public outcome
Plea accepted; probation and safety-course terms completed. No repeat offenses or later criminal filings were located.
Why it matters to the client
This is a real historical conduct issue, but not evidence of ongoing criminal instability by itself.
Innotech Corp. v. Peterson
Civil case search / county docket
Civil dispute tied to an alleged non-compete / confidentiality breach during the subject's move out of Innotech.
Public outcome
Settled in December 2018; no active post-judgment actions or related follow-on cases were found in the reviewed public sample.
Why it matters to the client
The matter suggests prior professional friction, but it does not appear to be an active operational problem today.
Court docket extract
17CV-482119Source sheet
Court docket capture
Filed note
Captured to preserve the docket sequence for the settled civil matter without relying only on narrative retelling.
Jurisdiction
Santa Clara County, California
Docket
17CV-482119
Reference
REC-02
Purpose
Civil dispute timeline
Innotech Corp. v. Peterson
Civil dispute tied to an alleged non-compete / confidentiality breach during the subject's move out of Innotech.
Mar 14, 2017
Complaint filed
Non-compete and confidentiality allegations attached to the subject's exit from Innotech.
Jun 2, 2017
Initial response
Defense appearance recorded; no injunctive emergency relief carried into the public docket.
Apr 19, 2018
Settlement conference
Court notes indicate private settlement discussions and continued continuances.
Dec 12, 2018
Dismissal after settlement
Case closed with no later public enforcement action found in the reviewed sample.
Analyst note
The matter suggests prior professional friction, but it does not appear to be an active operational problem today.
Document capture
Records and breach extract
Page 5
This capture combines the public-records findings with the breach table so the reader can see the two main trust concerns in the same evidence block.
- Includes the historical DUI and civil dispute context that shaped the records review.
- Shows the business-registration confirmation beside the legal and breach findings.
- Makes the record set feel sourced from an actual file, not just retold on the page.
Records review log
This excerpt shows the dated public-record checks that shaped the legal and financial readout.
2013-07-19
RecordsState criminal court records
Single misdemeanor DUI located in California; sentence completed with no repeat offenses found.
Why it mattered: This is a past concern, not evidence of current criminal instability on its own.
2018-12-12
RecordsCivil case search
Innotech Corp. vs. Peterson settled in December 2018 over an alleged non-compete issue.
Why it mattered: There is some professional-friction history, but nothing currently active.
2016-03-03
RecordsTax lien release history
IRS lien recorded in 2015 for $8,200 and released in 2016 after full payment.
Why it mattered: This is a historical financial issue, but not a sign of current active distress.
2025-11-28
RecordsFederal and state bankruptcy search
No bankruptcy filings or active monetary judgments located.
Why it mattered: There is no public sign of severe financial collapse.
Financial records
- Bankruptcy: no federal or state bankruptcy filings located for the subject in the reviewed public sweep.
- Tax lien: IRS lien for $8,200 recorded in 2015 and released in 2016 after full payment.
- Judgments: no active monetary judgments located in the reviewed county and statewide record layers.
- Property continuity: ownership traces align with long-term Bay Area residence and do not suggest distressed turnover.
What was not found
- No bankruptcy filings located.
- No active monetary judgments located.
- No active criminal proceedings beyond the historical DUI record.
Section
09
09 BUSINESS AND DOMAIN FOOTPRINT
Business and domain footprint
The consulting launch, domain traces, and public business identity belong together as one business-review block.
Business registration
The consulting entity that anchors the subject's latest career move.
Entity
Peterson Tech Consulting LLC
Jurisdiction
California
Registration date
October 5, 2025
Entity number
202565711824
Status
Active
Registered agent
James R. Peterson
Business email
Domain and infrastructure review
The public business surface tied to the new consulting identity.
Primary domain
petersontechconsulting.com
First observed
October 7, 2025
Registrar
Cloudflare Registrar
TLS
Active certificate observed at review time
Mail routing
Business email visible and routable from the public site
Site state
Single-page consulting site with limited firm history and no published client roster
Consulting site capture
Observed Nov 1, 2025Source sheet
Consulting website capture
Filed note
Captured after the LLC filing to verify that the consulting identity had a live public contact surface and matching domain.
Domain
petersontechconsulting.com
Observed
Observed Nov 1, 2025
Reference
BUS-02
Purpose
Business launch verification
Site title
Peterson Tech Consulting
Independent infrastructure advisory for cloud platforms, resilience, and executive technical review.
- Single-page site with no client logos or published case studies
- Business email and forwarding line are publicly visible
- No privacy policy or long-form company history present at review time
Public contact
[email protected] · +1 (415) 555-0456
Analyst note
The site looks real and current, but it still presents like a newly launched one-person consultancy.
Registry extract
Observed Oct 5, 2025Source sheet
Registry extract capture
Filed note
Captured to preserve the California filing details that tie the consulting launch to James R. Peterson by name and region.
Registry
California Secretary of State business search
Observed
Observed Oct 5, 2025
Reference
BUS-01
Purpose
Legal business anchor
Entity
Peterson Tech Consulting LLC
Entity number
202565711824
Status
Active
Filed
Oct 5, 2025
Agent
James R. Peterson
Principal region
San Francisco, California
- Registry timing aligns with the LinkedIn transition and the consulting-domain launch.
- The filing is the strongest legal anchor for the business identity.
Analyst note
The filing date, agent name, and principal region line up with the October 2025 profile transition and the consulting domain launch.
Business significance
- The LLC registration confirms the consulting move is operational, not just rhetorical.
- The domain and site launch create a new public-facing surface that did not exist before October 2025.
- The business identity is real but still early-stage, lightly built, and dependent on James's personal reputation.
- The current site supports legitimacy, but it does not yet show the footprint of a mature multi-client consultancy.
Business review log
These entries show when the consulting identity first became visible and which public surfaces confirm it.
2025-10-05
BusinessState business registry
Peterson Tech Consulting LLC registered with James R. Peterson as the registered agent.
Why it mattered: The consulting move appears genuine, not just social-media positioning.
2025-10-07
BusinessDomain registration / infrastructure review
petersontechconsulting.com was registered in early October 2025 with basic hosted infrastructure and TLS.
Why it mattered: The business rollout is real but still early and lightly built.
2025-11-01
BusinessConsulting website
The live site is a basic consulting landing page with contact points but no mature company footprint yet.
Why it mattered: This looks like a newly launched one-person consultancy, not an established firm.
Section
10
10 CYBER AND BREACH EXPOSURE
Cyber and breach exposure
Breach history, underground review, and security posture should be isolated so the risk is easy to understand.
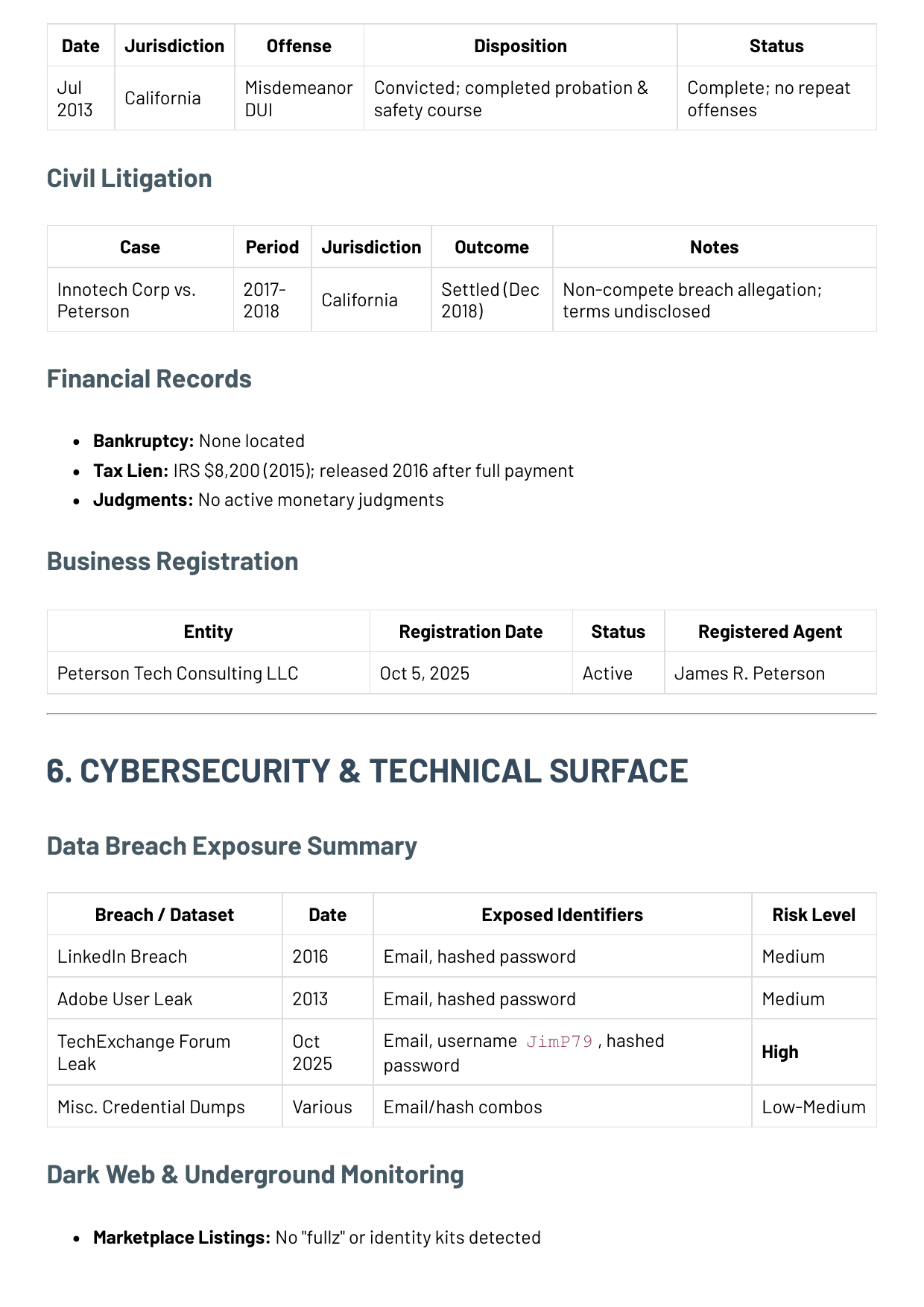
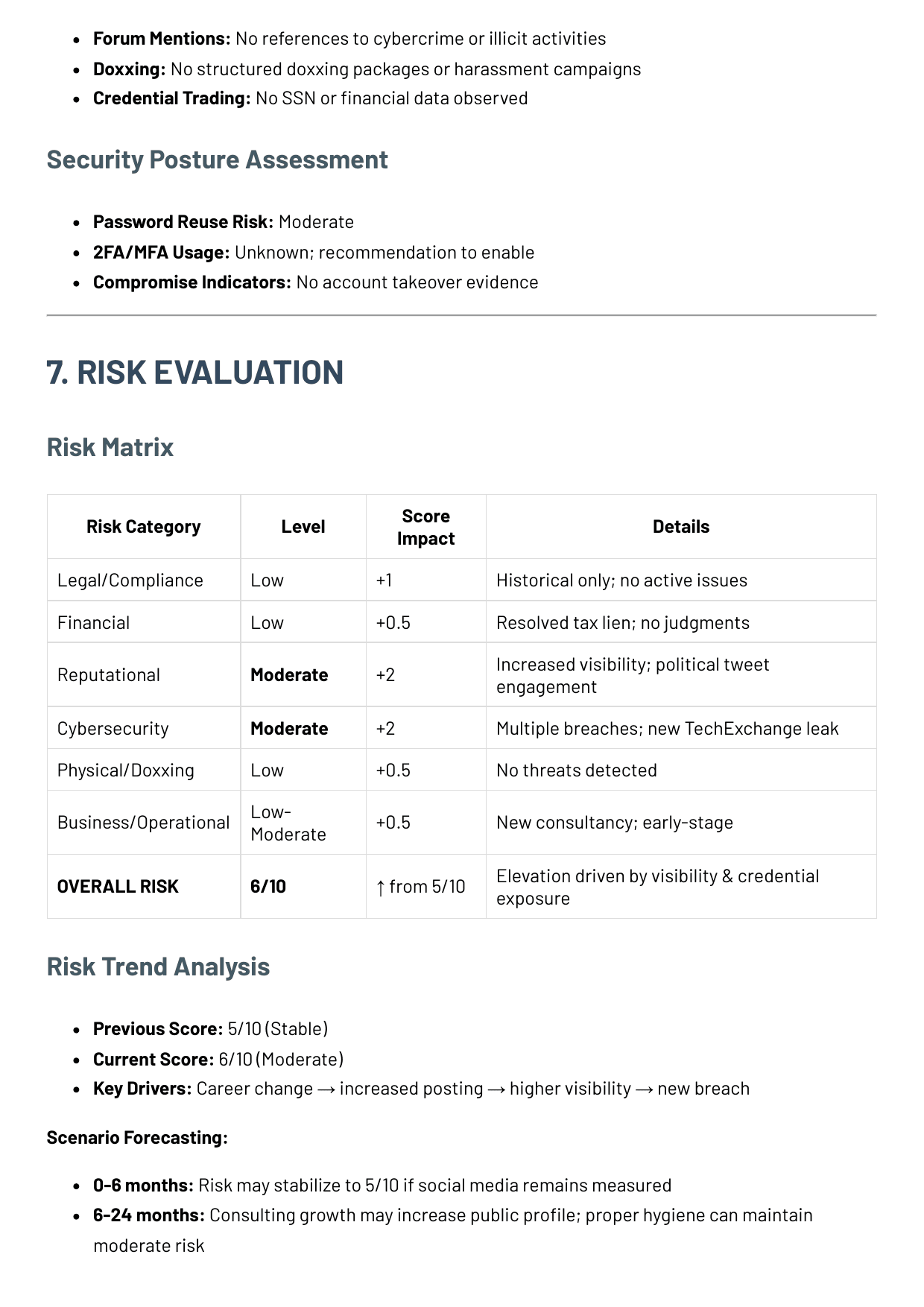
Dataset
Observed / source
Exposed identifiers
Current implication
LinkedIn breach
MediumMay 2016
Historical breach aggregators
Email and hashed password
Historical credential exposure only; still relevant because the same personal email persists across newer surfaces.
Treat as part of the long-term password-reuse pattern and reset any credential overlap.
Adobe user leak
MediumOct 2013
Historical breach aggregators
Email and hashed password
Older credential event that reinforces the pattern of repeated exposure on the same personal email.
Supports the recommendation for broad password rotation and MFA coverage.
TechExchange forum leak
HighOct 2025
TechExchange forum leak
Email, username JimP79, hashed password
Freshest cyber event in the file and the main reason the score moved upward during the monitoring window.
Immediate credential rotation and continuous leak monitoring are recommended.
Misc. credential mirrors
Low-MediumVarious
Mirrored credential dumps
Email and hash combinations
Adds repetition rather than a distinct new incident; useful mostly as evidence of persistent reuse risk.
Monitor for resurfacing and treat as cumulative evidence, not as a separate crisis event.
Source sheet
Breach extract capture
Filed note
Captured to preserve the October 2025 breach details that elevated the cyber risk picture above the older historical leaks.
Source
TechExchange leak review
Observed
Observed Oct 27, 2025
Reference
CY-03
Purpose
Freshest credential event
Identity under review
[email protected] / JimP79
Observed field
Value
Freshest dataset
TechExchange forum leak (Oct 2025)
Observed identifiers
Email, username, hashed password
Historical overlap
LinkedIn 2016, Adobe 2013
Current implication
Recent credential exposure during consulting launch window
- This is the event that moved the cyber score from background concern to active review item.
- The issue is current credential hygiene, not proof of live account compromise.
Cyber review log
This excerpt ties the breach table to dated exposure events and the practical account-risk meaning of each one.
2016-05-01
CyberHistorical breach aggregators
Personal email appears in the 2016 LinkedIn breach with hashed credential exposure.
Why it mattered: The subject is part of the common historical breach ecosystem, which increases account-hygiene importance.
2013-10-01
CyberHistorical breach aggregators
The same email address appears in the Adobe user leak.
Why it mattered: This is not unusual alone, but repetition raises the need for hygiene controls.
2025-10-27
CyberTechExchange forum leak
Email and username JimP79 appear in the October 2025 TechExchange leak.
Why it mattered: Recent credential exposure makes current account-hardening more urgent than the older leaks do.
2025-11-28
CyberDark web and underground monitoring
No full identity kits, doxxing packages, or targeted threat chatter located.
Why it mattered: There is exposure, but not evidence that the subject is currently being actively targeted.
2025-11-28
CyberGitHub repository review
No obvious public-secret or token leakage observed in the accessible repositories.
Why it mattered: The public code surface does not currently look reckless.
Dark web and underground monitoring
- Marketplace listings: no "fullz" or identity-kit packages located.
- Forum mentions: no references to cybercrime, extortion, or illicit activity.
- Doxxing: no structured doxxing packages or targeted harassment campaigns located.
- Credential trading: no SSN or financial data observed in indexed underground chatter.
Security posture assessment
- Password reuse risk: Moderate.
- 2FA / MFA usage: Unknown; analyst recommendation is to enable on all critical accounts.
- Compromise indicators: no account takeover evidence in the current sample.
Cyber response interpretation
- The breach picture matters because the same long-used personal email appears repeatedly across historical and recent datasets.
- The October 2025 TechExchange event is materially different from the older leaks because it is recent and overlaps with the consulting launch window.
- No direct account-takeover evidence or underground targeting package was found in the reviewed public sample.
- The most practical risk remains credential hygiene and exposure management, not evidence of an active attacker campaign.
Section
11
11 TIMELINE
Timeline
A believable consumer report should show the chronology of major identity, work, and risk events in one place.
2001-06
IdentityGraduated from UCLA
Computer science degree becomes the earliest stable career anchor.
2005-01
ProfessionalMoves into Bay Area engineering roles
Early software work begins the Los Angeles to San Jose transition.
2010-01
ProfessionalJoined Innotech Corp.
Long tenure at Innotech creates a verified mid-career anchor.
2013-07
RiskDUI conviction
Single historical criminal record; no repeat offenses located.
2015-01
RiskIRS lien recorded
Later released in 2016 after full payment.
2019-10
ProfessionalBecame CTO at TechNova
The most prominent professional identity phase in the public record.
2025-10-05
MonitoringPeterson Tech Consulting LLC registered
The central business-launch event behind the recent monitoring activity.
2025-10-15
MonitoringLinkedIn profile updated
Publicly reflects departure from TechNova and move to consulting.
2025-10-22
RiskX post draws elevated engagement
Most visible reputational-volatility event in the monitoring appendix.
2025-10-27
RiskTechExchange breach detected
Primary cyber-risk trigger that pushes the score from 5/10 to 6/10.
Section
12
12 RISK ASSESSMENT
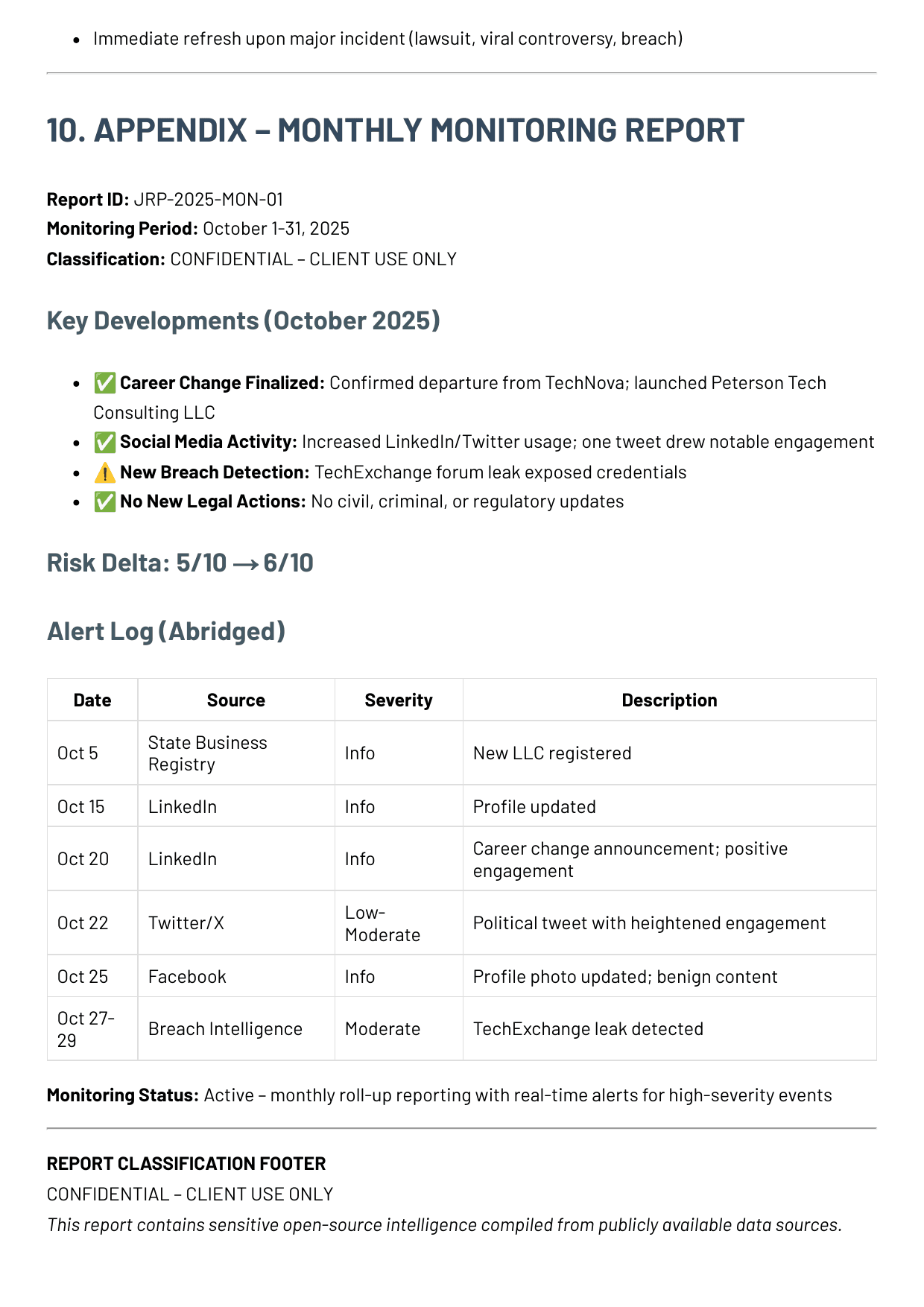
Risk assessment
Explain what the evidence means and why the final risk conclusion lands where it does.
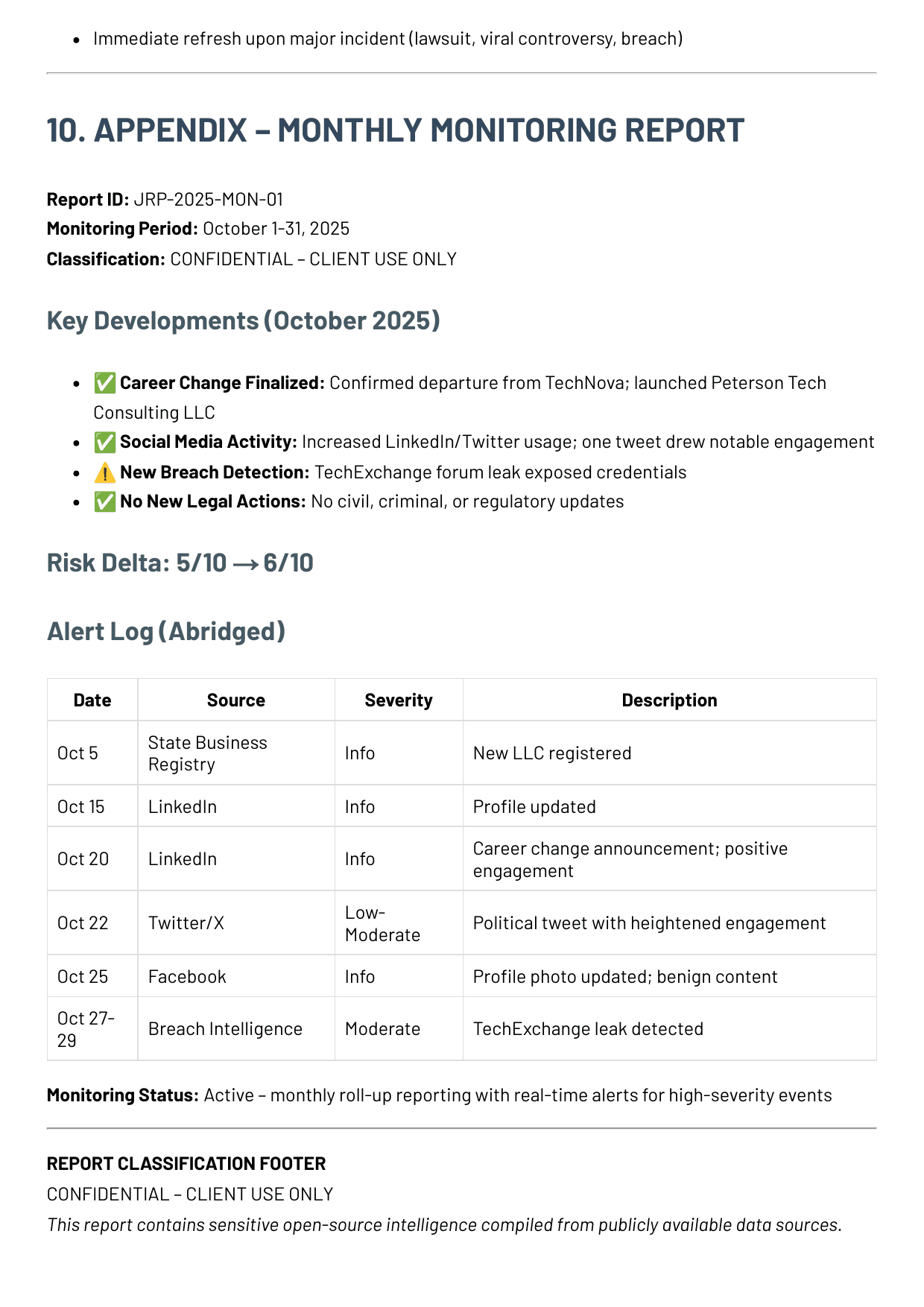
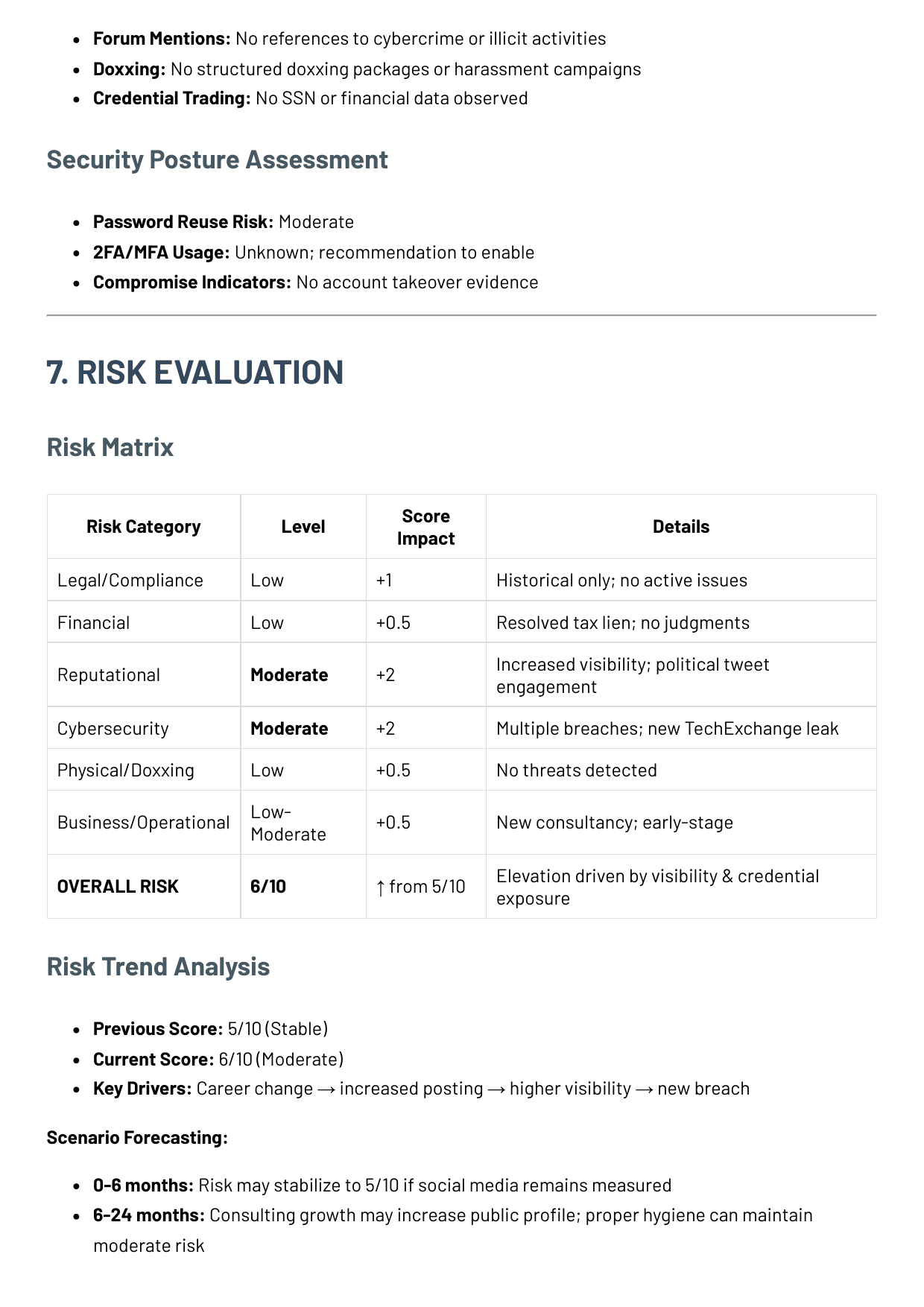
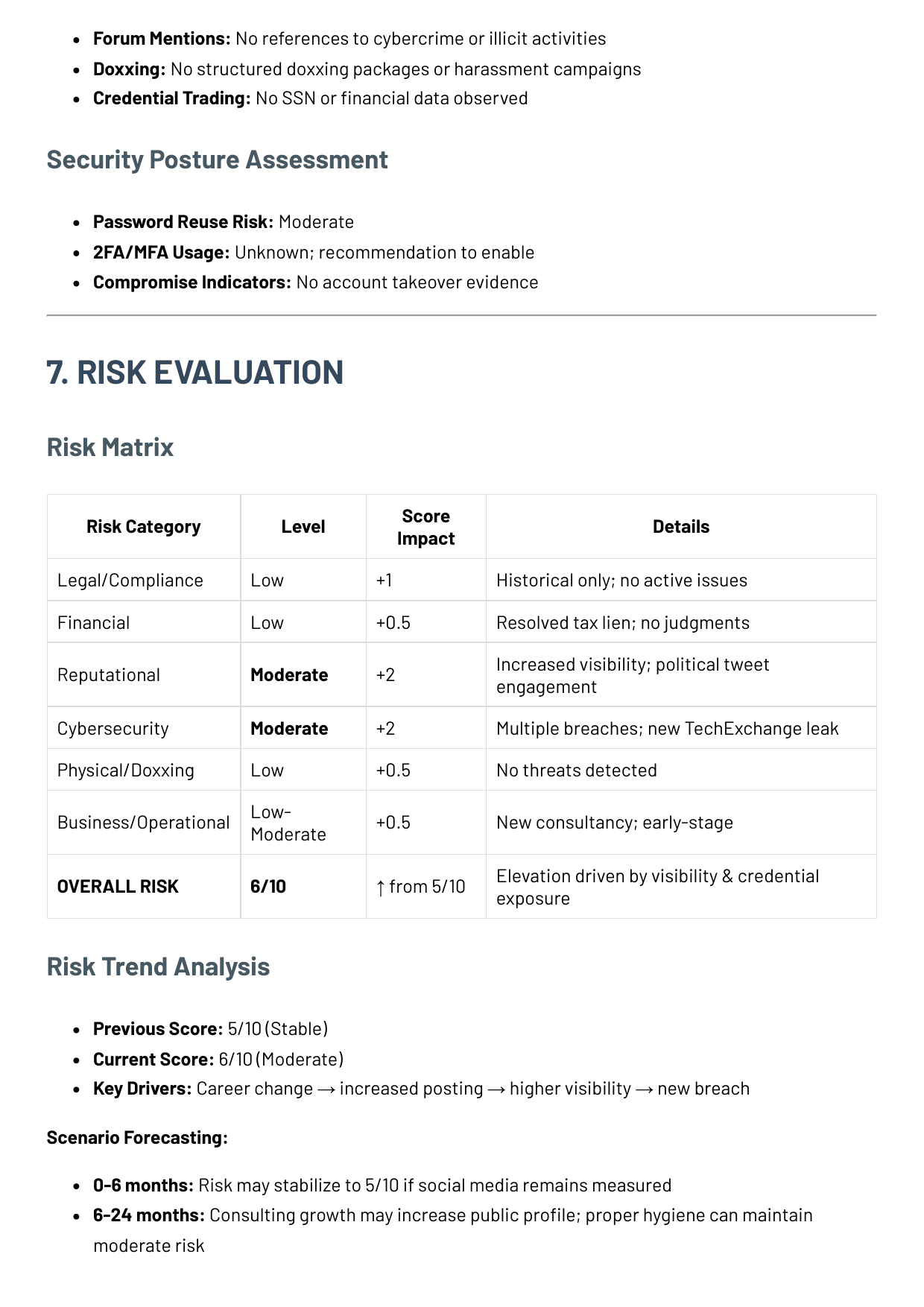
Risk category
Level
Impact
Details
Legal / compliance
Low
+1
Historical only; no active issues or repeat behavior located.
Financial
Low
+0.5
Resolved tax lien and no active monetary judgments.
Reputational
Moderate
+2
Increased visibility and polarizing commentary increased attention load.
Cybersecurity
Moderate
+2
Multiple historical breaches plus the October 2025 TechExchange event.
Physical / doxxing
Low
+0.5
No threats, address exposure campaigns, or targeting packages detected.
Business / operational
Low-Moderate
+0.5
New consultancy creates a fresh public attack and reputation surface.
Overall risk remains moderate at 6/10, up from the prior 5/10 baseline.
Risk trend
- Previous score: 5/10 (stable).
- Current score: 6/10 (moderate).
- Key drivers: career change -> more posting -> higher visibility -> new breach.
Scenario forecast
- 0-6 months: risk may return toward 5/10 if posting behavior stays measured.
- 6-24 months: consulting growth increases profile exposure; strong hygiene keeps risk manageable.
Document capture
Risk matrix from the source file
Page 6
The risk assessment section now has the same document anchor the reader would expect in a delivered report: the score, categories, and movement logic captured directly from the file.
- Shows the score movement from 5/10 to 6/10 in the source file itself.
- Makes the written conclusion easier to trust because the matrix is visible beside it.
- Helps the page feel like a reviewed dossier instead of only a stylized web summary.
Conclusion
- No hidden catastrophic liabilities surfaced in the sample open-source review.
- Residual risk is driven by credential exposure and the public-profile spike that came with the career transition.
- The monitoring appendix proves why recurring review matters after a Deep Search has been delivered.
Section
13
13 RECOMMENDED NEXT STEPS
Recommended next steps
End with practical actions for the client, not methodology or product explanation.
0-7 days
Priority 1 - Immediate controls
- Rotate credentials tied to [email protected] and any reused passwords.
- Enable MFA on primary email, social platforms, banking, and domain registrar access.
- Enroll the exposed email addresses in continuous breach and dark-web monitoring.
7-30 days
Priority 2 - Near-term posture hardening
- Separate personal and professional posting behavior and define a public-commentary policy.
- Harden the consulting business identity with dedicated mail, domain hygiene, and contact separation.
- Review public GitHub repositories for credentials, old tokens, or environment leakage.
1-12 months
Priority 3 - Ongoing monitoring
- Maintain monthly OSINT monitoring for news, breaches, social activity, and registry changes.
- Provide family OPSEC guidance to spouse and children for privacy-preserving posting habits.
- Prepare a lightweight crisis-response plan for identity theft, viral controversy, or doxxing attempts.
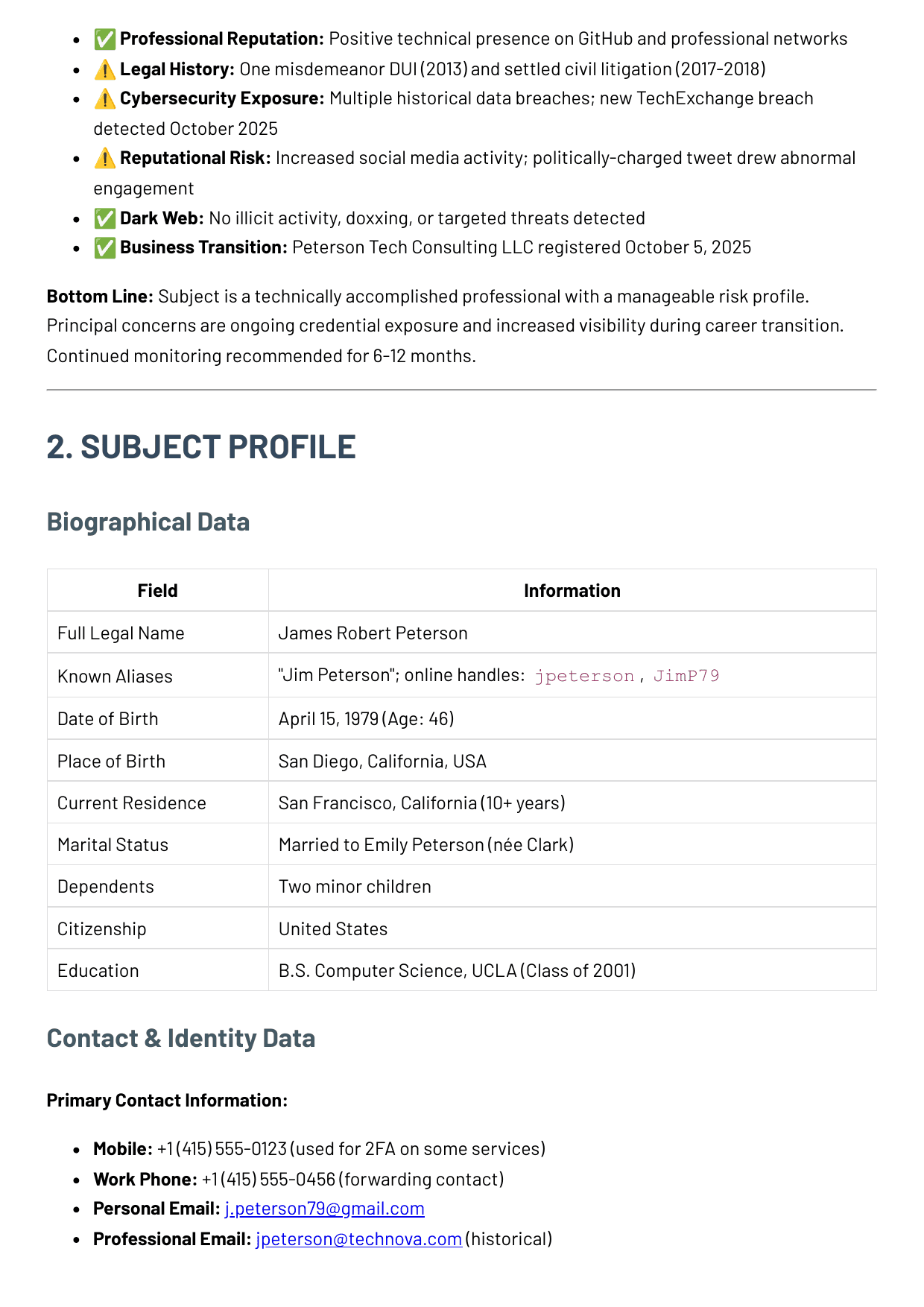
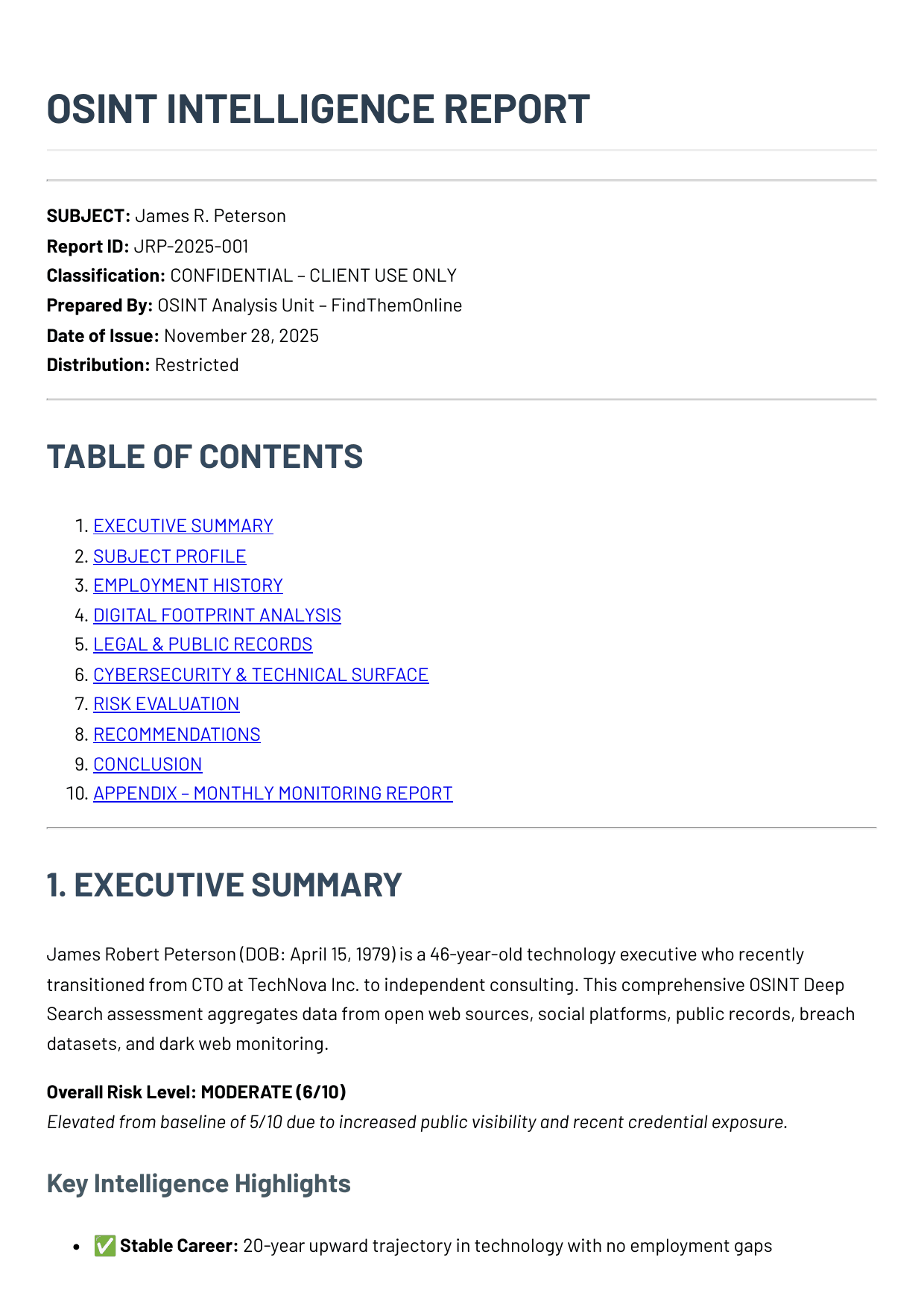
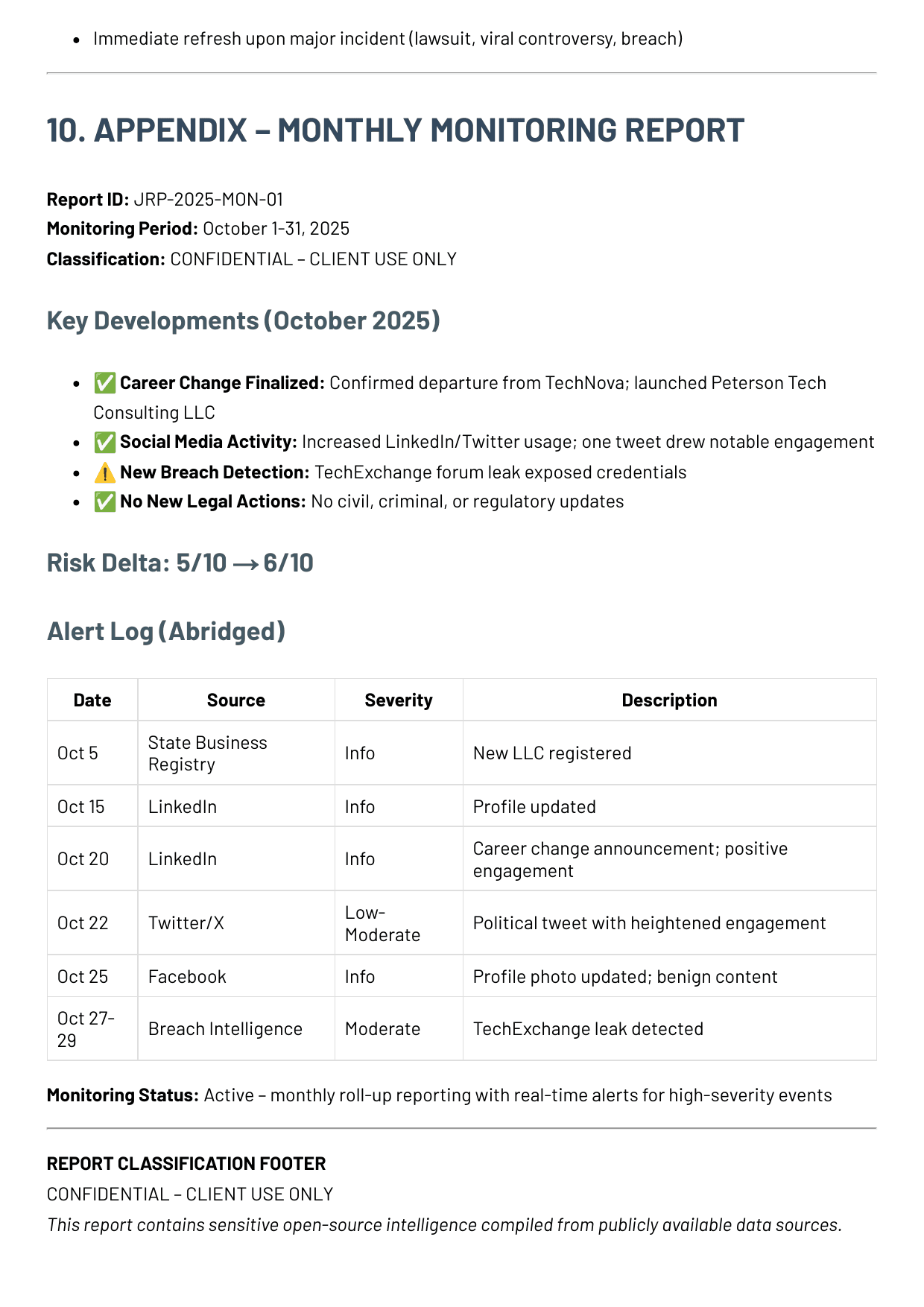
Why continued monitoring is recommended
Monitoring period: October 1-31, 2025. The monthly appendix proves how quickly visibility and breach events can change the trust picture after a baseline report is delivered.
Career change finalized
Departure from TechNova and the LLC launch were verified across multiple public surfaces.
Public activity increased
LinkedIn and X became more active after the consulting launch.
New breach detection
The TechExchange forum leak created the most material change in the monitoring window.
No new legal actions
No civil, criminal, or regulatory updates appeared during the October monitoring cycle.
Monitoring appendix alert log
Date
Source
Severity
Description
Oct 5
State business registry
New LLC registered and tied to the subject.
Oct 15
Profile updated to reflect the transition to consulting.
Oct 20
Career change announcement posted with positive engagement.
Oct 22
Twitter / X
Policy tweet drew elevated engagement and more contentious replies.
Oct 25
Profile photo refreshed; no adverse content attached.
Oct 27-29
Breach intelligence
TechExchange leak detected with identifiers tied to the subject.
Section
00
APPENDIX A REVIEW SCOPE
Appendix A: review scope and corroboration notes
This appendix records how the file was built, what source families were consulted, and where the scope limits sit. It stays outside the main decision path on purpose.
Appendix handling notes
- This appendix records how the file was built; it is not the main decision section of the report.
- Findings were only elevated when they survived corroboration across more than one surface or when a single authoritative record was decisive on its own.
- The source families below reflect the review breadth available to this case type, not a promise that every listed site will matter in every file.
- Protected medical records, bank records, device forensics, and law-enforcement-only data are outside scope unless separately authorized.
Representative sources reviewed
500+
Expanded case by case from the internal source registry and the subject's own pivots.
Internal review layers
36
Identity, social, records, business, technical, and monitoring layers were available to this case.
Corroboration rule
Cross-verified
Findings were carried forward only when they held across more than one surface or one authoritative record was decisive.
Monitoring cadence shown
Monthly
The appendix includes the October monitoring cycle used to track post-baseline change.
Cross-source corroboration excerpt
These log entries show how the file conclusion holds across identity, records, business, cyber, and negative-news review.
2025-10-15
ProfessionalLinkedIn profile
LinkedIn profile reflects the move from TechNova CTO to Peterson Tech Consulting with 500+ connections.
Why it mattered: His work history appears real and professionally legible rather than improvised.
2025-10-05
BusinessState business registry
Peterson Tech Consulting LLC registered with James R. Peterson as the registered agent.
Why it mattered: The consulting move appears genuine, not just social-media positioning.
2018-12-12
RecordsCivil case search
Innotech Corp. vs. Peterson settled in December 2018 over an alleged non-compete issue.
Why it mattered: There is some professional-friction history, but nothing currently active.
2025-10-27
CyberTechExchange forum leak
Email and username JimP79 appear in the October 2025 TechExchange leak.
Why it mattered: Recent credential exposure makes current account-hardening more urgent than the older leaks do.
2025-11-28
RecordsNews and media search
No major adverse news, fraud reporting, or scandal coverage located beyond normal career references.
Why it mattered: There is no public-signals pattern of major scandal or repeated public controversy.
Identity discovery and pivot engines
Multiply identifiers, verify aliases, and connect people-search, school, and genealogy trails.
Internal layers
M1, M6, M10, M23, M24, M33
Typical refresh cadence
Front-loaded in Deep Search; revisited weekly or monthly for drift.
- Google, Bing, DuckDuckGo, Intelligence X, Internet Archive
- Whitepages, Spokeo, BeenVerified, FastPeopleSearch, Radaris
- Have I Been Pwned, DeHashed, Hunter.io, reverse-username hubs
- FamilySearch, yearbook archives, alumni directories, official gazettes
Social, messaging, and public reputation
Track identity density, sentiment, message communities, and public narrative risk.
Internal layers
M2, M3, M4, M17, M29, M31
Typical refresh cadence
Daily or weekly depending on visibility and volatility.
- Facebook, Instagram, X, TikTok, LinkedIn, Reddit, YouTube
- Telegram channels, Discord servers, WhatsApp public communities
- Hacker News, Stack Overflow, niche forums, complaint boards
- Google News, local archives, press wires, community bulletins
Records, courts, and business verification
Validate address continuity, litigation, licensing, corporate roles, and official filings.
Internal layers
M7, M8, M9, M11, M12, M36
Typical refresh cadence
Weekly to monthly, with event-driven checks during active matters.
- Property and tax assessor portals, business registries, procurement datasets
- PACER, RECAP, CourtListener, county clerk portals, appellate databases
- OpenCorporates, SEC EDGAR, Companies House equivalents, chamber rosters
- Regulatory registers, official gazettes, public contract repositories
Media, movement, and lifestyle exhaust
Connect image traces, reviews, travel patterns, marketplaces, clubs, and address continuity.
Internal layers
M13, M14, M15, M16, M25, M30
Typical refresh cadence
Weekly for volatile surfaces; monthly for long-tail records.
- Google Lens, Bing Visual Search, Yandex Images, TinEye, EXIF extractors
- Google Maps reviews, Yelp, TripAdvisor, Strava, Meetup, Eventbrite
- Aircraft registries, marina rosters, club pages, auction catalogs
- Airbnb hosts, Craigslist archives, Upwork, race results, HOA minutes, MLS mirrors
Technical, infrastructure, and underground risk
Map code footprint, domains, certificates, wallets, leak appearances, and dark-web chatter.
Internal layers
M18, M19, M20, M21, M27, M28
Typical refresh cadence
Daily for breach and leak surfaces; weekly for infrastructure drift.
- GitHub, GitLab, package registries, container registries, dev blogs
- Etherscan and other on-chain explorers when relevant
- Ahmia, Haystak, ransomware leak blogs, breach aggregators, Tor dump mirrors
- WHOIS, passive DNS, CT logs, reverse IP, Shodan, Censys
Long-tail specialist and authorized sources
Cover academic, trade, adult-alias, medical-authorized, and scientific traces when the subject warrants it.
Internal layers
M5, M22, M26, M32, M34, M35
Typical refresh cadence
Usually monthly or case-driven; medical sources only when authorized.
- ResearchGate, ORCID, conference directories, university staff lists
- OnlyFans / Fansly and alt-identity communities when relevant
- Trade associations, standards bodies, thesis repositories, think-tank reports
- Hospital portals, PubMed, ClinicalTrials.gov, institutional repositories
Client action note
This reference file shows the structure and density of a delivered review.
When a live subject needs this level of work, the baseline deliverable is a Deep Search case. Monitoring is added only when the file stays active and the risk picture keeps moving.
- A live Deep Search is the baseline deliverable when a client needs this level of review on a real subject.
- Monitoring is only added when the subject remains active, public visibility is rising, or new breach and reputation events keep changing the trust picture.
- If the file needs to support a decision in motion, start with the baseline case and escalate only where the evidence keeps moving.
Section
06
06 SOCIAL MEDIA ACTIVITY
Social media activity
Public behavior, posting patterns, and narrative volatility should be reviewed as their own surface, not hidden inside a broader footprint section.
X / Twitter
@JimPeterson
This is the public channel most likely to change the subject's reputation quickly if posting cadence or tone shifts.
Facebook
James Peterson
Facebook contributes more to identity continuity and household context than to active reputational risk.
Instagram
@james.peterson
Dormant accounts still matter because they help rule out obvious hidden activity or conflicting public personas.
Supporting social traces
These traces confirm which public surfaces are active, quiet, or worth watching more closely.
X / Twitter profile
Medium confidenceThe @JimPeterson account shows approximately 1,260 followers and higher posting activity in October 2025.
He is public enough that attention and controversy can now travel faster.
X / Twitter post on Oct 22, 2025
Medium confidenceA policy-oriented post drew elevated engagement and more hostile replies than the baseline.
There is some narrative risk if public posting becomes more frequent or more divisive.
Facebook profile
Low confidenceProfile photo updated in late October with no additional adverse content in the visible public layer.
The account looks real but low-signal; it does not add material concern by itself.
Instagram profile
Low confidenceDormant account with limited public content and no meaningful activity since 2018.
There is no obvious hidden second life here, but also not much current evidence.
Observed social activity
These are the public moments that changed the subject's visibility and reputational exposure during the October 2025 window.
Oct 15, 2025
LinkedInProfile update
Profile changed from TechNova CTO to independent consultant.
This is the cleanest professional pivot in the file and the beginning of the visibility increase.
Oct 20, 2025
LinkedInCareer-transition post
Public "moving on" announcement generated strong positive engagement from the subject's professional network.
Supports the legitimacy of the transition and shows the new consulting identity was publicly recognized.
Oct 22, 2025
X / TwitterPolicy commentary post
A policy-oriented post triggered more hostile and polarized replies than the baseline.
This is the most important reputational-risk event in the monitoring window.
Oct 25, 2025
FacebookProfile photo update
Profile image refreshed with no associated public controversy or notable comment trail.
Low-risk continuity signal only; useful more as a verification point than as a behavior signal.
X / Twitter post review
Observed Oct 22, 2025Source sheet
X post capture
Filed note
Captured to preserve the Oct 22, 2025 post that generated the sharpest reply spike in the monitoring window.
Surface
X / Twitter post review
Observed
Observed Oct 22, 2025
Reference
SM-03
Purpose
Reputation volatility check
@JimPeterson
1,260 followers
Replies
84
Reposts
41
Likes
178
Analyst note
Reply tone shifted more hostile than the subject's earlier October activity. This was the clearest reputational-volatility event in the monitoring window. The post does not show direct misconduct, but it increased public attention quickly.
Social interpretation
Document capture
Monitoring appendix and alert log
Page 8
This appendix image is where the social and visibility story becomes concrete: platform updates, the Oct 22 X event, and the breach alert all sit in one reviewed monthly record.